Cyber surveillance is no longer the forte of intelligence agencies. Many tools can access and monitor your computer, laptop, smartphone, tablet, etc. So, you may wonder if someone can see a laptop screen without permission, how that may happen, and whether or not it is legal.
Technically, someone can see a laptop screen without permission if a backdoor is set up with remote access, such as an application or software. Legally, someone can’t see your laptop screen unless it is an employer, a parent, a proctor, or a law enforcement officer.
The legality and technicalities aren’t generic or universal due to the scope of cyber surveillance and the objectives of someone seeing a laptop screen without the permission of the user.
Protect yourself with counter surveillance devices.
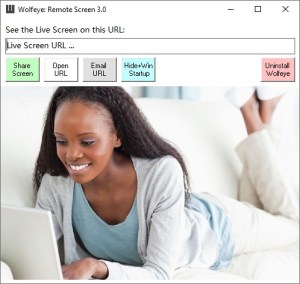
Your employer can see what you’re doing on your work laptop that is owned by the company. A parent can see what a child is doing on a laptop or other device at home. Colleges, schools, and universities may see what their students are doing on their computers and laptops on campus. They only need to install a computer monitoring software like “Wolfeye Remote Screen” to see the computer live screen or make screenshots on a regular basis. That will allow to remotely spy on the computer.
These monitoring and surveillance measures aren’t necessarily confined to campuses, offices, or workplaces. Employers can see what employees are doing on their laptops at home or on the move. Likewise, invigilators or proctors can conduct real-time surveillance during online exams.
Employers Can Legally Monitor Company Laptops and Phones
Company laptops and phones aren’t personal property. So, employers don’t require permission per se from their employees to see what they are doing on these laptops and phones. The laws of different countries aren’t identical, but workplace monitoring or surveillance is legal worldwide.
Since workforces in many industries operate remotely or work from home nowadays, companies can use monitoring and surveillance software or a suite of tools for different purposes, including:
- Accounting
- Administration
- Management
- Operations
- Productivity
- Security
The scope of such surveillance may include personal laptops if the devices are used for official work. However, employers generally need to inform their employees about any software or tools being used on personal devices. Written consent is usually necessary for such monitoring.
Even company laptops and phones are typically put under surveillance after disclosing the fact that such devices will be monitored by the employer. These disclosures and written consent are normally included in the stack of appointment or contract papers of employees and freelancers.
That said, employers aren’t legally obligated to inform their employees or freelancers if they are monitoring company laptops. Consider the example of the 1986 Electronic Communications Privacy Act (ECPA) in the United States. The provisions cover the following privacy concerns:
- Communications: electronic, oral, and wire
- Data: personal information on laptops, etc.
- Storage: personal information in servers, etc.
However, none of these provisions extend to official communications and workplace activities. A company has the right to see what every employee is doing on a laptop during active hours. The surveillance may be 24/7 for company laptops and during work hours for personal devices.
Some companies use surveillance tools that are evident on monitored devices through an active interface, notifications, etc. But employers can use hidden applications, such as remote screen monitoring software. Not alerting an employee can be vital for various types of assessments.
The extent and nature of workplace surveillance and how employers go about monitoring their company laptops and phones may change in the future if the relevant laws are amended or new provisions are included.
For instance, the California Consumer Protection Act doesn’t require employers to disclose their data collection and usage or workplace monitoring practices to their employees. But the law has made it mandatory for all businesses or companies to disclose their policies to consumers.
This exemption for employers is in effect until 2023. The law may not change. But if it does, the employers in California will be legally obligated to disclose more about their monitoring practices to the employees. The Massachusetts Information Privacy Act has similar provisions.
However, neither of these two nor other potential laws seek to prohibit workplace monitoring. The purpose of such evolving laws is to ensure that employees aren’t subject to excessive and unethical surveillance practices.
Online or Remote Examinations Using Laptops Are Monitored
Invigilators or proctors of online examinations use different types of tools to monitor the laptops of examinees, whether they are onsite or remote. These tools usually go beyond seeing a user’s laptop screen, such as the following:
- Live audio feed to detect any sound in the setting that may indicate cheating.
- Live webcam feed to monitor the examinee and the surroundings in real-time.
- Network surveillance to check the examinee’s browser and internet activities.
- Screen monitoring to watch how the examinee is navigating the online test.
These monitoring tools are used for the duration of the examination, but they are mandatory in most cases, even if an examinee is using a personal laptop. That said, examinees provide their permission to the relevant authority or invigilator unless the device is a school computer.
Parents Can Supervise Their Children’s Activities on Laptops
Parents have the legal right to supervise their minor children’s activities on any device, including laptops. So, any parent can see what a child is doing in real-time and also archive the activities if necessary. These activities include all offline and online usage of a laptop, phone, tablet, etc.
Laptops Using Public Networks Are Vulnerable to Surveillance
Public networks don’t necessarily snoop on laptop screens or record whatever a user may do on a personal device. But connecting to public networks makes a personal laptop accessible to any type of surveillance, which isn’t necessarily a monitoring program for security purposes.
Administrators of public networks generally limit their monitoring to data usage. But unprotected or unsafe public networks can make laptop communications without end-to-end encryption quite vulnerable to hacking, including but not limited to the following places:
- Airports
- Cafes
- Colleges
- Hotels
- Offices
- Public buildings
No permission is sought by public networks to see what you’re doing on your laptop since the operator or owner of that infrastructure has the legal right to maintain the security of the facility. Also, hackers can use backdoors to see what you’re doing on your laptop on a public network.
Hackers use a myriad of ways to establish a backdoor, which can give them remote access to your laptop through:
- Data interception
- Internet browsing
- Keystroke logging
- Microphone access
- Screen mirroring
- Webcam feed
While hacking is illegal, hackers don’t seek permission to see what you’re doing on your laptop. Even if your inadvertent action leads to the initial hack and setting up of the backdoor, you don’t consciously give permission per se to anyone who might be a part of the hacking operation.
Employers and academic institutions can see an official company or school laptop screen without permission, but they can’t see personal devices, unless there’s written consent. Parents can see their children’s laptop screens without permission by installing remote access software that’s hidden but running in the background.
This content was originally published here.