In the fast-paced world we live in today, security is a top concern for individuals and organizations alike. When it comes to keeping yourself and your assets safe, it’s crucial to be one step ahead of potential threats. That’s where covert surveillance detection tools come into play. These cutting-edge tools are designed to help you identify and prevent any covert surveillance or spying activities that may be directed towards you. By utilizing these advanced technologies, you can maximize your security and gain peace of mind, knowing that you have the upper hand in protecting what matters most.
What are Covert Surveillance Detection Tools?
Covert surveillance detection tools are essential elements in modern security systems that are designed to detect and counteract covert surveillance activities. These tools are used to protect sensitive information, prevent espionage and unauthorized access, and maintain privacy and confidentiality. By utilizing physical and digital surveillance detection tools, organizations can enhance their security measures and effectively respond to potential threats.
Definition and Types
Covert surveillance detection tools encompass a range of techniques and technologies that aid in the detection of surveillance activities. These tools are designed to uncover hidden threats and gather intelligence to counteract them effectively. There are two main categories of covert surveillance detection tools: physical surveillance detection tools and digital surveillance detection tools.
Importance of Maximizing Security
In today’s technology-driven world, maximizing security is of utmost importance. Organizations need to prioritize security measures to protect sensitive information, prevent espionage and unauthorized access, and maintain privacy and confidentiality. By implementing covert surveillance detection tools, businesses can fortify their security infrastructure and stay ahead in the ever-evolving landscape of threats.
Securing Sensitive Information
Sensitive information is the lifeblood of many organizations. Whether it’s trade secrets, intellectual property, or customer data, safeguarding this information is crucial for maintaining a competitive edge and ensuring business continuity. Covert surveillance detection tools play a vital role in detecting potential breaches and protecting sensitive data from falling into the wrong hands.
Preventing Espionage and Unauthorized Access
Covert surveillance is often employed by individuals or groups attempting to gain unauthorized access to sensitive areas or information. It is a common tactic used by corporate spies, criminals, and even state-sponsored actors. By utilizing surveillance detection tools, organizations can detect and deter potential espionage attempts, safeguarding their assets and preventing unauthorized access.
Maintaining Privacy and Confidentiality
Privacy and confidentiality are paramount for maintaining trust and credibility with clients, customers, and stakeholders. Covert surveillance detection tools help organizations maintain this critical aspect of their operations by ensuring that confidential communications and activities remain secure and uncompromised. By effectively detecting and countering surveillance activities, organizations can safeguard their privacy and preserve the trust of those they interact with.
Categories of Covert Surveillance Detection Tools
Covert surveillance detection tools can be broadly categorized into two main categories: physical surveillance detection tools and digital surveillance detection tools. Each category serves a different purpose and requires specific techniques and technologies to effectively detect and counteract covert surveillance activities.
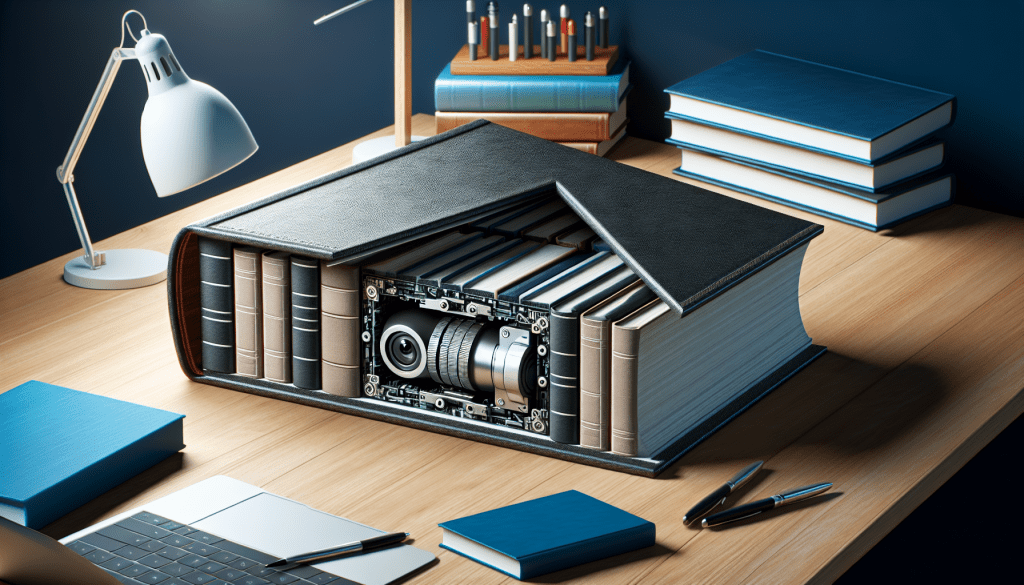
Physical Surveillance Detection Tools
Physical surveillance detection tools involve techniques and technologies that aid in the identification and detection of physical surveillance activities. These tools can include physical security measures, observation techniques, and counter-surveillance measures.
Digital Surveillance Detection Tools
Digital surveillance detection tools, on the other hand, focus on identifying and countering the surveillance activities that occur in the digital realm. This includes cybersecurity measures, network monitoring tools, and data analysis techniques that help organizations detect and respond to cyber threats and unauthorized access attempts.
Physical Surveillance Detection Tools
Introduction
Physical surveillance detection tools are an essential part of any comprehensive security strategy. These tools enable organizations to detect and respond to physical surveillance activities effectively. By implementing physical surveillance detection measures, organizations can proactively address potential threats, protect their physical assets, and ensure the safety of their personnel.
Counter-Surveillance Measures
Counter-surveillance measures are critical for identifying and countering physical surveillance activities. These measures involve a variety of techniques aimed at detecting and neutralizing potential surveillance threats. Examples of counter-surveillance measures include conducting regular security sweeps, evaluating suspicious behavior, and using technical surveillance countermeasures (TSCM) to detect hidden surveillance devices.
Familiarization with Surroundings
Being familiar with one’s surroundings is essential for effective physical surveillance detection. Security personnel should have a detailed understanding of the layout and characteristics of the area they are tasked with protecting. This familiarity allows them to identify and respond to potential surveillance activities more efficiently.
Observation Techniques
Observation techniques are another crucial aspect of physical surveillance detection. Security personnel should be trained in effective observation techniques to identify suspicious behavior and potential surveillance threats. This can include techniques such as surveillance detection routes, identifying surveillance indicators, and maintaining situational awareness.
Digital Surveillance Detection Tools
Introduction
In the digital age, the importance of digital surveillance detection tools cannot be overstated. As cyber threats continue to evolve, organizations must utilize these tools to protect their digital assets and ensure the integrity and confidentiality of their data. Digital surveillance detection tools encompass a range of technologies and techniques aimed at identifying and countering digital surveillance activities.
Cybersecurity Measures
Cybersecurity measures form the foundation of digital surveillance detection. These measures include robust firewalls, intrusion detection systems, and encryption protocols to safeguard digital information from unauthorized access. By implementing thorough cybersecurity measures, organizations can effectively detect and counter potential digital surveillance threats.
Network Monitoring Tools
Network monitoring tools play a critical role in digital surveillance detection. These tools allow organizations to monitor network traffic, identify suspicious activities, and detect potential cyber threats. By analyzing network logs and traffic patterns, security personnel can promptly respond to digital surveillance attempts and mitigate potential risks.
Data Analysis Techniques
Analyzing data is another crucial aspect of digital surveillance detection. By employing data analysis techniques, organizations can uncover patterns, anomalies, and potential indicators of digital surveillance activities. This analysis can involve automated algorithms or manual review of logs and data, allowing security personnel to detect and respond to threats effectively.
Developing an Effective Security Strategy
Developing an effective security strategy is essential to maximize the benefits of covert surveillance detection tools. While these tools are valuable, they must be part of a broader security approach that addresses vulnerabilities, implements necessary measures, trains personnel, and establishes response protocols.
Identifying Vulnerabilities
Before implementing covert surveillance detection tools, organizations must first identify their vulnerabilities. Conducting a thorough security audit can help uncover weaknesses in physical and digital security systems, allowing for targeted implementation of appropriate surveillance detection measures.
Implementing Covert Surveillance Detection Tools
After identifying vulnerabilities, organizations can select and implement the covert surveillance detection tools that best address their specific needs. It is crucial to consider factors such as compatibility with existing security systems, scalability, ease of use, and cost-effectiveness when choosing the appropriate tools.
Training Security Personnel
Equally important is the training of security personnel in the effective use of covert surveillance detection tools. They need to be knowledgeable about the technologies and techniques involved, as well as be aware of potential indicators and response protocols. Ongoing training and knowledge updates are vital to maximizing the effectiveness of surveillance detection tools.
Establishing Response Protocols
Furthermore, organizations must establish response protocols in the event of surveillance detection. These protocols should outline the appropriate steps to take when suspicious activities are identified and provide clear guidance on escalation procedures and communication channels. Having well-defined response protocols ensures a swift and coordinated response to potential threats.
Factors to Consider When Choosing Covert Surveillance Detection Tools
When selecting covert surveillance detection tools, organizations must consider several factors to ensure the effectiveness and compatibility of the chosen tools within their existing security infrastructure.
Compatibility with Existing Security Systems
Covert surveillance detection tools should seamlessly integrate with existing security systems to avoid any operational disruptions. Compatibility ensures that the tools can effectively communicate with other security measures and provide a holistic surveillance detection solution.
Scalability and Upgradability
As security needs evolve, organizations must choose surveillance detection tools that can scale and adapt to changing requirements. Scalability and upgradability allow for the addition of new features and capabilities, ensuring that the tools remain effective in the face of emerging threats.
Ease of Use and Integration
Covert surveillance detection tools should be user-friendly and easy to integrate into existing security operations. Complex tools can be challenging to implement and maintain, requiring extensive training or specialized personnel. Therefore, simplicity and ease of use are crucial in maximizing the effectiveness of surveillance detection tools.
Cost and ROI Analysis
Cost-effectiveness is an important consideration when selecting covert surveillance detection tools. Organizations should conduct a thorough analysis of the costs involved, including the purchase, installation, maintenance, and training associated with the tools. Additionally, considering the return on investment (ROI) ensures that the chosen tools provide significant value in relation to the benefits they offer.
Best Practices for Maximizing Security
While covert surveillance detection tools are effective in enhancing security, organizations must also implement best practices to maximize their effectiveness. These best practices include regular security audits, continuous monitoring and evaluation, information sharing and collaboration, and staying up-to-date with technological advancements.
Regular Security Audits
Regular security audits assess the effectiveness of existing security measures and identify potential vulnerabilities. By conducting periodic audits, organizations can proactively address any weaknesses and ensure that their surveillance detection tools remain up-to-date and reliable.
Continuous Monitoring and Evaluation
Continuous monitoring and evaluation of security systems are key to detecting and responding to evolving threats. By regularly analyzing system logs, network traffic, and other relevant data, organizations can identify abnormalities and potential surveillance activities, allowing for prompt response and remediation.
Information Sharing and Collaboration
Information sharing and collaboration with other organizations are essential in combating surveillance threats. By sharing information on new surveillance techniques, indicators, and countermeasures, organizations can collectively stay ahead of potential threats and enhance their own security strategies.
Keeping Up with Technological Advancements
The landscape of covert surveillance technology is continually evolving. Organizations must remain up-to-date with the latest technological advancements to effectively detect and counter potential surveillance threats. Staying informed about emerging trends and technologies ensures that organizations can adapt their security strategies accordingly.
Emerging Trends in Covert Surveillance Detection Tools
As technology advances, new trends in covert surveillance detection tools continue to emerge. Organizations must stay aware of these trends to effectively address potential threats and maintain a robust security posture.
Artificial Intelligence and Machine Learning
Artificial intelligence (AI) and machine learning (ML) are revolutionizing the field of covert surveillance detection. These technologies allow for automated analysis of vast amounts of data, enabling the detection of complex surveillance patterns and anomalies that may otherwise go unnoticed. AI and ML-based surveillance detection tools offer enhanced accuracy and efficiency, contributing to more effective security strategies.
Automation and Smart Surveillance Systems
Automation plays a significant role in covert surveillance detection. With the integration of automation capabilities, security systems can monitor and detect potential surveillance activities in real-time, giving organizations a proactive advantage in countering threats. Smart surveillance systems with advanced sensors and analytics further enhance the effectiveness of surveillance detection, allowing for quick response and mitigation.
Internet of Things (IoT) Integration
The proliferation of IoT devices presents new opportunities and challenges in covert surveillance detection. By integrating IoT devices into security systems, organizations can gather more data and enhance their ability to detect potential surveillance threats. However, this integration also introduces additional avenues for potential vulnerabilities and requires robust security measures to mitigate associated risks.
Conclusion
In today’s complex and technology-driven world, maximizing security is of utmost importance. Covert surveillance detection tools offer organizations a comprehensive approach to identify and counteract potential surveillance threats. By implementing physical and digital surveillance detection tools, organizations can protect sensitive information, prevent espionage, and maintain privacy. To ensure the effectiveness of these tools, organizations should implement best practices, stay informed about emerging trends, and continuously evaluate and adapt their security strategies. With a robust security posture and effective surveillance detection tools, organizations can stay one step ahead of covert surveillance activities and protect their assets, information, and personnel.